Mein Name ist Markus Schumacher, Jahrgang 1973, und ich wohne im Kreis Bergstraße (Hessen). In diesem Blog tausche ich mich zu Themen aus, die mich seit vielen Jahren im wahrsten Sinn des Wortes “beschäftigen”: Technologie, Unternehmertum und “Spielzeuge”. Dieser Beitrag skizziert, wie ich dazu gekommen bin.
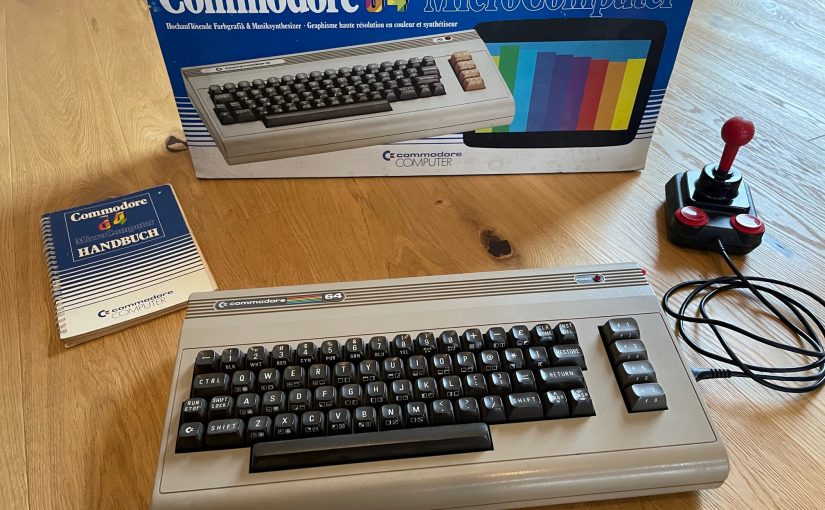
Schon als Kind haben mich Computer fasziniert. Der bewusste Startschuss meiner Nerd-Karriere war 1985, als mir meine Eltern einen Commodore C64 geschenkt haben. Neben Spielen hat mich auch schnell das Gestalten mit einem Computer fasziniert und das tut es bis heute. Den C64 habe ich übrigens auch noch (siehe Beitragsbild).
Dieses Hobby führte mich zu einem Studium der Elektrotechnik an der TU Darmstadt. Als ich dann 1996 in den Semesterferien keinen vernünftigen Job gefunden habe, beschloss ich an einem Programmierpraktikum teilzunehmen, um die damals neue Sprache Java zu lernen. Nach Assembler und C im Studium, war das eine ganz neue Erfahrung und hat weitere Weichen für die Zukunft gestellt. Denn mit diesen Kenntnissen ausgestattet, habe ich schnell einen Job bei einer Werbeagentur in Frankfurt bekommen, um dort erste Applets für Seiten von Finanzfirmen zu konzipieren einzubauen.
Derart infiziert beschloss ich, an der Uni zu bleiben und zu promovieren. Das habe ich 1998 am IT Transfer Office (ITO) begonnen, einer Organisation des Fachbereichs Informatik der TU Darmstadt, die sich ausschließlich durch extern finanzierte Projekte am Leben erhielt, zu Beginn von der Digital Equipment Corporation gesponsert. Dies hat die unternehmerische Ader meines Ichs geweckt. Die gestalterische Freiheit, aber auch das unternehmerische Risiko (kein Projekt, kein Job, keine Promotion) dieser Zeit hat mich sehr geprägt. Sie hat mir auch früh bewusst gemacht, dass Technik alleine nicht reicht, um Produkte oder Dienstleistungen am Markt zu vertreiben.
Ohne Lehrverpflichtung fehlte mir jedoch der Kontakt zu den Studenten. Ich habe daher aufbauend auf meinen Kindheitserfahrungen mit Computern den Hacker Contest ins Leben gerufen. Ziel war, damals aktuelle Technologien (damals neu: WLAN, Bluetooth, etc.) zu untersuchen. In Teams haben die Teilnehmer dabei abwechselnd die Rolle von Angreifer und Verteidiger eingenommen. Diese Initiative wurde viele Jahre fortgeführt, auch nachdem ich die Uni längst verlassen habe.
Im Mai 2003 habe ich meine Promotion “mit Auszeichnung” erfolgreich abgeschlossen. Thema waren Security Patterns, ein Thema, mit dem ich mich viele Jahre auseinander gesetzt habe. Patterns kommen ursprünglich aus der Architektur. Der Gedanke ist, dass kein Architekt lernen kann, wie man schöne Häuser baut. Dazu braucht es Erfahrung – und genau das wird in einem Pattern festgehalten. Die Idee wurde auf Software übertragen (sgt. Design Patterns) und ich habe es dann für Security adaptiert und beschrieben.
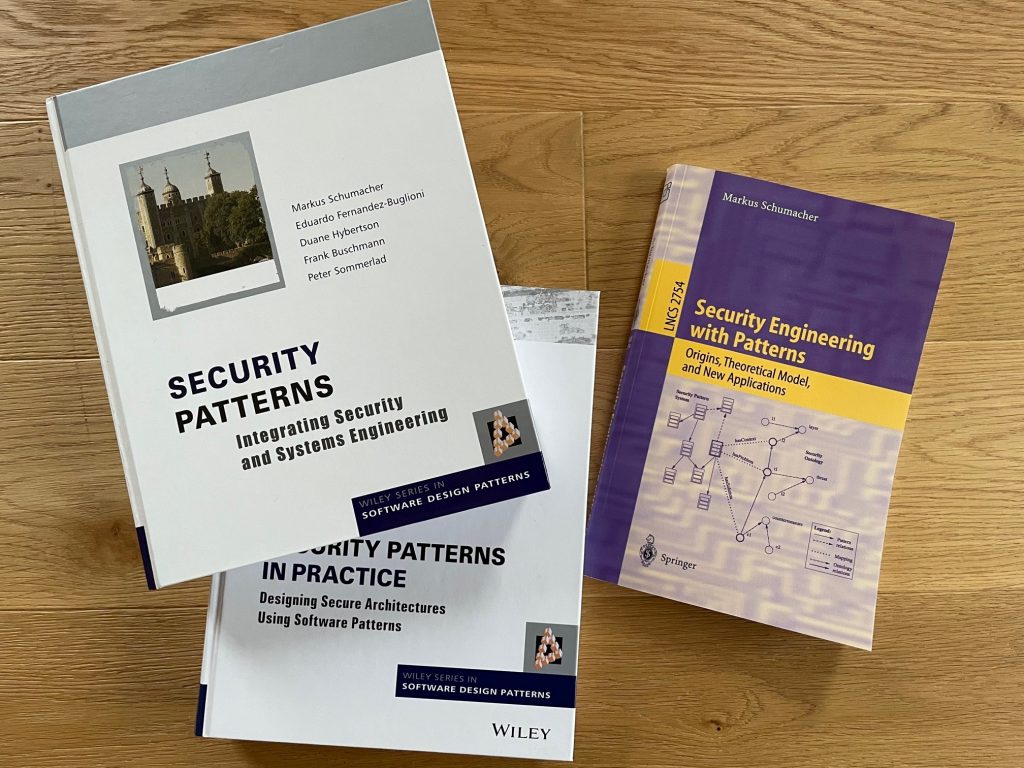
Mit diesem Know-How ausgestattet, habe ich mich entschieden, nach der Promotion “raus” zu gehen. Ich hatte zwar das Angebot für eine Juniorprofessur, aber das war damals noch recht neu und für mich nicht sehr attraktiv. Ich habe daher meiner ITO Kontakte genutzt und fand schnell eine Anstellung bei SAP als Product Manager für Security. SAP war damals ein weiterer Projektpartner des ITO und hatte das Lab in Karlsruhe übernommen, mit dem wir kooperiert hatten. In dieser Zeit wurde die “alte” SAP Basis in NetWeaver (Release 640+) umgebaut und ich habe in der Zeit sehr viel über die unterschiedlichen SAP Technologien lernen dürfen, zuletzt dann auch bei dem Umbau von einer Idee zum generell verfügbaren Produkt SAP Business ByDesign.
Das Thema Security war und ist mir seit vielen Jahren eine Herzensangelegenheit. Ich habe es allerdings nicht im Sinne einer Funktion zum Schutz verstanden, wie etwas mit Name und Passwort anmelden. Es war für mich vielmehr immer spannender zu verstehen, welche Lücken ein System hat, wie man diesen ausnutzen kann und was man tun muss, um “schussfest” zu sein. Da ich zudem festgestellt habe, dass SAP Kunden sehr viel selbst entwickeln, war der nächste Schritt vorprogrammiert. Wenn programmiert wird und wenn die Systeme komplex sind, kommt es fast zwangsläufig zu Lücken. Somit stand fest, dass ich die SAP 2006 verlasse und gemeinsam mit einem Geschäftspartner, den ich bei SAP kennengelernt habe, die Virtual Forge GmbH gegründet habe. Viele der ersten Mitarbeiter, die dann erstmal SAP fokussierte Penetrationstests durchgeführt haben, habe ich übrigens aus den Jahrgängen der Teilnehmer des Hacker Contest rekrutiert.
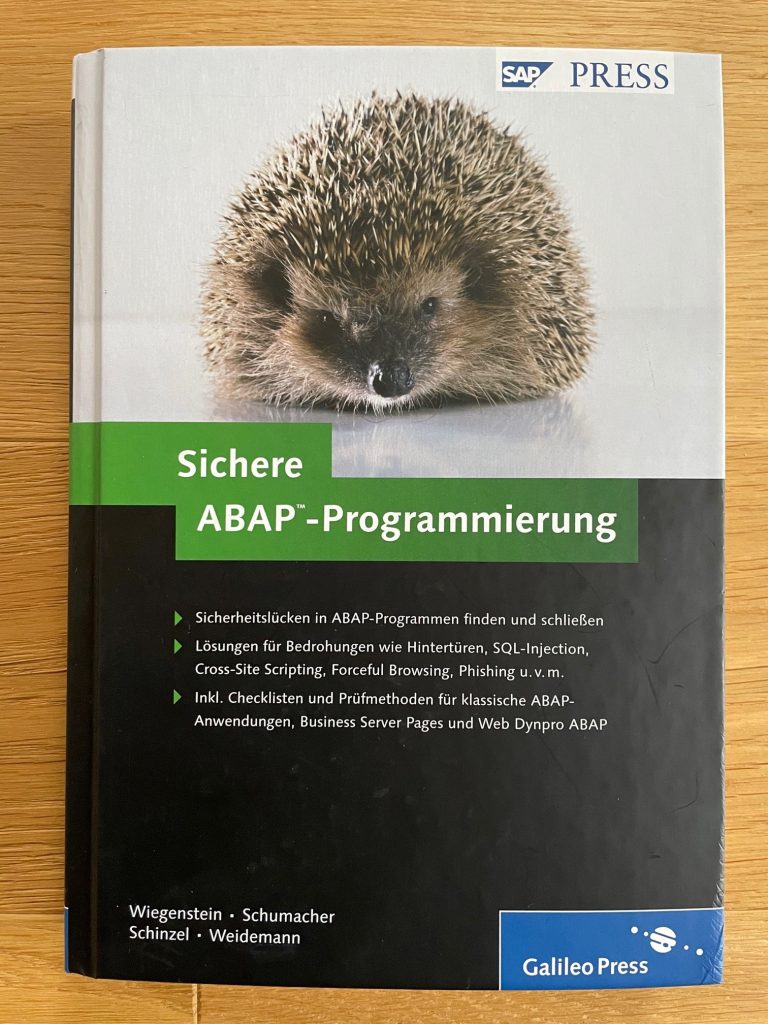
Mit im Gepäck hatte ich einige Ideen, was sich im SAP Umfeld alles tun lässt, dass nicht vom SAP Standard angeboten wird. Daraus ergab sich ein weiteres Pionierthema: Scanning von SAP ABAP Code nach Sicherheitslücken. Die daraus entstandene Lösung CodeProfiler für ABAP (Version 1.0 vorgestellt auf der SAP TechEd in Berlin im Jahr 2009) ist bis heute eine marktführende Lösung. In dieser Zeit wurde auch unser Buch “Sichere ABAP Programmierung” veröffentlicht. An Aktualität hat es nicht viel verloren, denn es gibt zwar einige neue Programmierkonstrukte im SAP Umfeld, aber “old-school” ABAP ist längst nicht am Ende.
Virtual Forge war für mich die praktische Einführung in die Betriebswirtschaft. Ausschließlich selbst-finanziert ist es uns gelungen, die Firma über die Jahre immer wieder neu zu erfinden, um am Markt vorne zu bleiben und überleben zu können. Als CEO und Geschäftsführer habe ich mich viele Jahre um den Vertrieb (wie verkaufe ich den Wert von Technologie), Marketing (welche Kunden spreche ich an und wie finden diese zu mir) und die Administration gekümmert. Dabei mussten immer wieder harte Entscheidungen getroffen und der eigene Kompass neu justiert werden: dazu gehörte die Firmenstrategie und deren Umsetzung. Mit ca. 120 Mitarbeitern haben wir 2018 beschlossen, uns auf die Suche nach Wachstumskapital zu machen, um strategisch (vs. reaktiv) vorgehen zu können. Dies endete schließlich mit dem Verkauf der Firma (Mitte 2019) an den Marktbegleiter Onapsis, dort war ich als General Manager Europe erstmals seit vielen Jahren wieder Angestellter.
Seit Anfang 2021 bin ich nun wieder selbstständig mit der Idee, Erfahrungen zu teilen, die ich auf dem hier dargestellten Weg zum Unternehmer gesammelt habe. Es geht wie eingangs geschrieben alle Facetten des Unternehmertums und technische Themen. Ich werde immer auch mal “Spielzeuge” neben dem Beruf beschreiben. Damit meine ich Dinge, die man sich als Erwachsener leisten kann und die vor allem eins machen: Spaß.